I assigned my Technology and Culture students to read part of Finn Brunton’s excellent book Spam: A Shadow History of the Internet. In it, he discusses the roots of 419 scams—what we often refer to as “Nigerian prince” scams, due to the prevalence of scammers using the narrative that they were a Nigerian prince unable to transfer funds. Brunton writes:
These are… an enormous narrative about the failures of globalization from which you, the reader, can profit. … From letters and telegrams in a world of newspapers to email messages in a 24-hour news cycle, 419 works where the spammer’s capacity to generate evidence exceeds our individual capacity to evaluate it—given some willful suspension of disbelief. (Brunton, 2013)
Brunton traces 419 fraud’s history back to the earlier “Spanish prisoner” scam, a similarly-shaped funnel for greed that played on a vague British awareness of turmoil in Spain by promising the reader they could financially benefit by helping a woman imprisoned there by the king:
Geographically, it plays on the remoteness and romance of a location, … it draws strength from current events, particularly war and political chaos—situations in which it is plausible to imagine unlikely fortunes and desperate bargains.” (ibid)
He later continues:
On the recipient’s side, it takes a deeply cynical (if ill-informed) understanding of politics—not necessarily Nigerian, as the messages are often set in other presumably chaotic and corrupt environments, such as Russia or American-occupied Iraq—that views the world as including these covert, corrupt machinations from which you are finally in a position to profit. … We can see the whole shape around 419 now… except for one part, the use of Google and other search engines as a corroborating source for producing authenticity. (ibid)
One of my most thoughtful students (who I’ll call Cybele) read this, and responded in her weekly discussion post:
I am really fascinated by the "remoteness" that Brunton talks about. I thought that it made sense historically, that the story presented was situated in a place far away from the scam's recipient, somewhere that was beyond the reach of the recipient so it was impossible to "fact-check." However, how about in today's world, where technologies are constant reminders of one's relationship to the wider world, in a way that what is going on in the physical remoteness is very much connected and relevant to us—how come the "remoteness" of these scams still remains relevant to the legitimacy of the scam? Brunton also notes the supporting document that provides validity for the scam, but I think the material by itself is no longer sufficient. rather, it is a constant, continuous network of discussion of the remoteness that ultimately gives credibility to the scam. That is, one newspaper or website about a political crisis would not likely to persuade the recipient that this political fallout is real. However, the constant portray of the instability/underdevelopment/etc. make the recipient the scam appear seem plausible. (from our class discussion board)
Building on her elaboration from the reading, I asked my students: When we use Google and digital news sources to understand people far from us, what is missing?
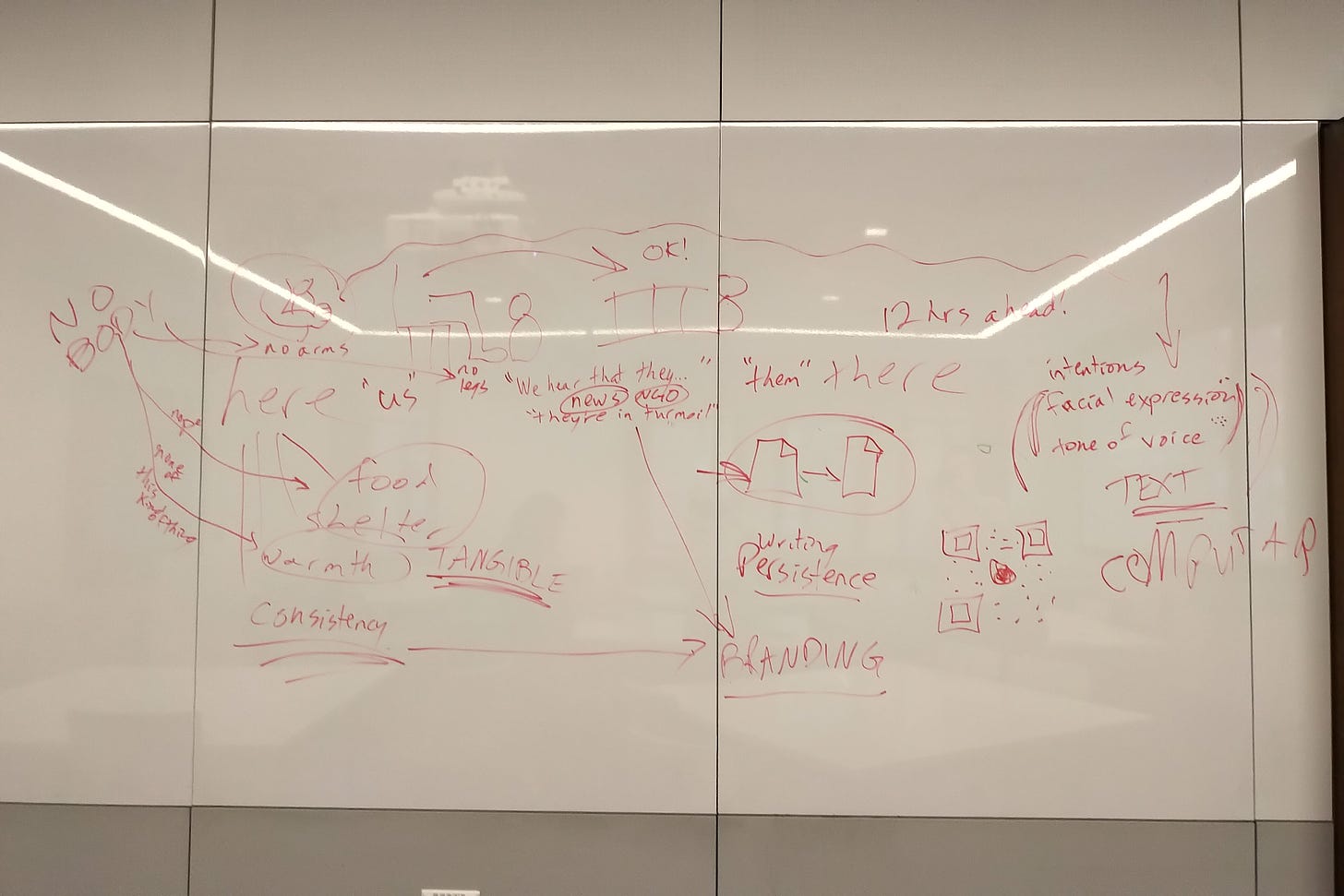
I began drawing one of my weekly maps of the connections between people, institutions, nature, technologies—which I tend to think of as systems maps, but which I’m certain look like the unhinged ravings of a conspiracy theorist to subsequent groups in that classroom who weren’t there for the discussion. (A few of my students have taken to photographing them after class; others, to meditatively erasing them.)
Over here: “us.”
Over there: “them.”
What is missing, I asked, in “our” understanding of “them”?
They went first to Cybele’s point, and Finn’s: what we do have is news narratives. Stories that build on earlier stories about “those people in turmoil;” shaped by and with Western-slanted narratives we’ve been discussing all semester about who is “backwards” and who is making “progress,” about who is manifestly destined by God to move into “uninhabited” land and whose existence is thereby denied.
And the medium that these scam messages arrived in: what does it afford us?
Well, it’s text.
How do we come to trust text?
We’d covered that some in the readings for two previous weeks: Michael Clanchy, writing about the English shift to documentary legal system with the invasion of the Normans in 1066. The English were skeptical: you put a date on a document to inspire trust? Isn’t that maybe sacreligious, when we’re living in Messianic time where Jesus was here yesterday and is coming back tomorrow? How many crosses or signatures or seals will make this document trustworthy, anyway? Brunton again, this time his book about money, discussing contracts and printed banknotes. And Brian Street, a sociolinguist and father of New Literacies scholarship, discussing how different ways of reading and writing are socially situated. Fijians in one era rejected the insistently Biblical literacy practices of missionaries and instead adapted reading and writing to traditions passed down in their communities over generations.
In shorthand: humans collectively and locally agree on the ways they will trust what is written.
But let’s get more basic than that, I exhorted my students. Outside of writing: how do humans come to trust?
The students paused in thought, then remembered they’re studying in a school of education, where developmental psychology is never far from reach. Your needs get met, said one of my students. Your parents feed you, they cuddle you, they keep you safe and warm.
And they do that over and over, I added.
Right, said the student. Consistently.
And if they don’t, the child’s ability to trust is substantially damaged, as Bruce Perry describes in The Boy Who Was Raised As A Dog, I went on. When I decided I needed to look further into research on how trust comes to be, I found a nice little volume with an overview of the literature over at the TC library (Linda Weber and Allison I. Carter, The Social Construction of Trust.) That tied in some other literature, from anthropology: Margaret Mead’s stages of childhood.
I started to draw (poorly) some representations of Mead’s stages at the top of the map: lap child, knee child, yard child. As the child thus begins to venture further from their parents, Weber and Carter’s book on trust points out, parents instruct the child on who or what is to be trusted as they venture out into the village, to the corner store, into the wilds: that person over there is to be trusted for their wisdom; that one sells safe food; be careful of strangers, of people who aren’t like us over here. Stereotypes get built into this; our brains do the pattern-recognition things that brains do.
So how does the trust we build in the people we see around us translate, in a world where humans can now perceive human beings who are thousands of miles away from them? This is where Cybele’s question and the stuff about writing comes in: people come to agreements about what qualities a document must have in order to be trustworthy. They treat these qualities of the document as stand-ins for attributes of the people they trust.
Does this remind you of anything? (I fish for answers too much when I’m trying to lead discussions.) I guide my students back to our earlier lesson about Mr. Coffee, Apple computers, and branding. Branding, according to Weber and Carter’s book, has also been developed as a means to extend trust beyond the people we can see around us, to mass audiences. The consistency of a logo and a graphic identity promise the viewer that the product they’re going to get is of the same quality they’ve come to trust through their local, personal experience.
Did I mention the deep-fryers at McDonalds? (A few nods. It’s one of my favorite rants.) Part of McDonalds’s mechanism for building brand loyalty is standardizing the food production process. Everything in a McDonalds kitchen has been measured and tweaked and standardized within an inch of its life. The fries are cut to a uniform width; the oil maintained at a specific temperature; the employee immerses the fries in the oil, a timer sets; it goes off, they take them out; and that’s how people have come to trust that no matter where they go in the world, McDonalds fries are going to be as close to a uniform crispy golden brown as humans doing food science and time and motion labor studies could possibly make them.1
So those Golden Arches mean standardized experience. And standardization means consistency—and that’s what our brains seek, and it’s what built trust as we were growing.
But what’s wrong with trusting a logo in the age of the internet?
My students look blank. They were too young to be Extremely Online in the first decade of the Aughts, so they missed the Yes Men convincing hapless marks that they were actually Dow Chemical or the World Trade Organization by scraping the look and feel of their websites, setting up camp at some plausibly similar web addresses, and fielding requests for press conferences in which they announced that the WTO was dissolving itself and Dow was going to take full fiscal responsibility for the Bhopal disaster.
I draw 📄→📄 on the board.
COPY/PASTE, I exhort my students. This is what computers facilitate that their forerunner media couldn’t make possible: it’s much easier to make copies of things. So late-20th-century assumptions about trusting the visual elements of branding have been disturbed. This is a key tool for online scammers—it’s fiendishly difficult to stop anyone from slapping a familiar logo on a phishing email or malicious ad.2
What else is missing? I ask my students. We’ve established that the trust that past generations had in branding has been disturbed. When we see people somewhere else through the media, digital or otherwise, what’s missing? What’s between us and them?
Time zones, one of them volunteers. They may be hours apart from us.
Right! I say, running a long arrow across the map. What they’re going through right at this very moment may be very different contextually. It may be the middle of the night where they are, the middle of the day here. In the opposite hemisphere, it’s the opposite season.
But let’s focus on our understanding of distant others when we only understand them through text. What’s missing?
Intentions, my students volunteer. Facial expressions. Tone of voice.
Right! Now they’re getting it. I return to the other side of the map and start annotating what we discussed earlier about development of trust among children. What else is missing from our understanding of distant others through media:
NO BODY
no arms to hold the lap child
no knee for the knee child to grapple on to
no connection to the food and shelter each of us would die without
no warmth—
none of this kind of thing, I scrawl down the board. None of what our species evolved to need.
So, Cybele, do we have tools now for rethinking our media “connectedness,” and why it might not be sufficient to overcome the difficulties of remoteness? I ask.
Cybele nods, thoughtfully taking it in. This summer, she will go halfway around the world, to study a modern empire and how it manages the people on its peripheries, how it tries to insist to them that they are all part of the same national project despite differences in language, and other distances.
Barbara Garson, The Electronic Sweatshop, 1988.
And don’t listen to any naïve techno-solutionist who tells you the copying ability of technology will by its sheer nature revolutionize how artists make a living, kids, goes another rant I’ve served them at least once. I sing them a bar or two of Nina Paley’s anti-copyright propaganda ditty “Copying is not Theft.” That was a narrative promulgated by tech enthusiasts in the early Aughts—it was a legitimate fight for change to media systems, and the allies of artists fought valiantly to see change—but we see where that ended up: for example, Spotify paying musicians a crappy per-stream rate. The tens of thousands of college students sued by the RIAA in 2009 for sharing on Napster and Limewire, some of them still in debt to this day for that. It was a weaponized legal maneuver aimed at changing the assumptions of a whole generation about who had what rights and who ought to get paid. In the end, the established media monopolies still had the money and the lawyers to wipe challenges to their monopolies off the map.